Secure Shell (SSH) is a widely used network protocol that allows users to securely access remote servers and manage their files. By default, SSH uses port 22 for communication, which can sometimes pose a security risk if left unchanged. In this blog post, we will explore how to change the SSH port on Rocky Linux to enhance the security of your server. We’ll also cover some essential steps to ensure that your server remains accessible after the change.
Why Change the SSH Port?
Changing the default SSH port can help reduce the likelihood of automated attacks and brute-force attempts on your server. By moving away from the default port, you make it harder for malicious users to guess the correct port for SSH access.
Dealing with Failed Login Attempts on Linux Servers
As a system administrator, you may often come across messages like “There were failed login attempts since the last successful login.” These messages can be concerning, as they may indicate unauthorized access attempts on your server.
Step-by-Step Guide How to Change SSH Port on Rocky Linux
Follow these steps to change the SSH port on your Rocky Linux server:
- Update your system: Before making any changes, it’s always a good idea to update your system. Run the following command:
sudo dnf updateInstall a text editor: If you haven’t already, install a text editor like Vim to modify the SSH configuration file.
Open the SSH configuration file: Open the /etc/ssh/sshd_config file with your preferred text editor:
sudo vim /etc/ssh/sshd_config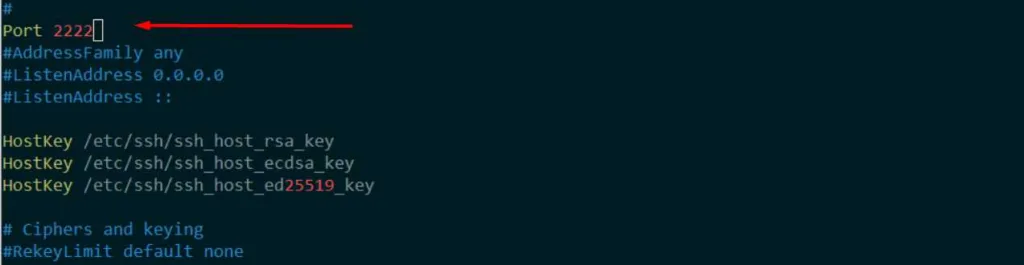
Change the SSH port: Find the line that starts with #Port 22. Uncomment it by removing the # symbol and change the port number to your desired value. For example, change it to Port 2222. Save and exit the file.
Configure the firewall: Update your firewall settings to allow the new SSH port. Use the following command, replacing 2222 with your chosen port number:
sudo firewall-cmd --permanent --zone=public --add-port=2222/tcpThen, reload the firewall to apply the changes:
sudo firewall-cmd --reloadRestart the SSH service: Restart the SSH service to apply the new configuration:
sudo systemctl restart sshdTest the new SSH port: From another machine, attempt to connect to your server using the new SSH port. Remember to replace your_server_ip and 2222 with your server’s IP address and chosen port number, respectively:
ssh -p 2222 user@your_server_ipIf the connection is successful, you have successfully changed the SSH port on your Rocky Linux server.
Troubleshooting Tips
If you encounter any issues after changing the SSH port, consider the following tips:
- Make sure you have allowed the new port through your firewall, as described in step 5.
- Double-check the syntax and formatting in your
/etc/ssh/sshd_configfile. - Ensure that no other services are using the port you have chosen for SSH.
- Check the SSH service status with
sudo systemctl status sshdto see if there are any errors.
Additional Security Measures
Changing the SSH port is just one way to enhance the security of your Rocky Linux server. You should also consider implementing other security measures, such as:
- Using SSH key authentication instead of passwords.
- Disabling root login and creating a separate user account for SSH access.
- Setting up a firewall to protect your server from unauthorized access.
- Regularly updating and patching your server to fix security vulnerabilities.
Conclusion
Changing the default SSH port on Rocky Linux is an essential step to enhance your server’s security. By following the steps outlined in this guide, you can easily modify the port and protect your server from automated attacks and brute-force attempts. Don’t forget to implement additional security measures to further strengthen your server’s defenses.
For more information on managing and securing your Rocky Linux server, check out these articles:
- How to Set Up an OpenVPN Server on Rocky Linux
- How to Install KVM Virtualization on Rocky Linux
- How to Install PostgreSQL on Rocky Linux
- How to Set Up RAID 1 on Rocky Linux
- Differences Between RAID 1 and RAID 0
Stay tuned for more articles on Rocky Linux, and don’t hesitate to share your thoughts and experiences in the comments below.